| |
|
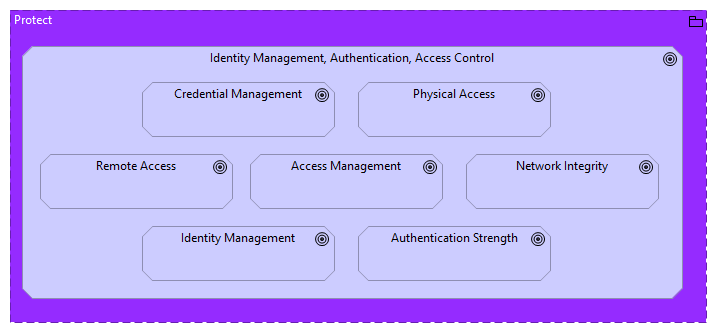
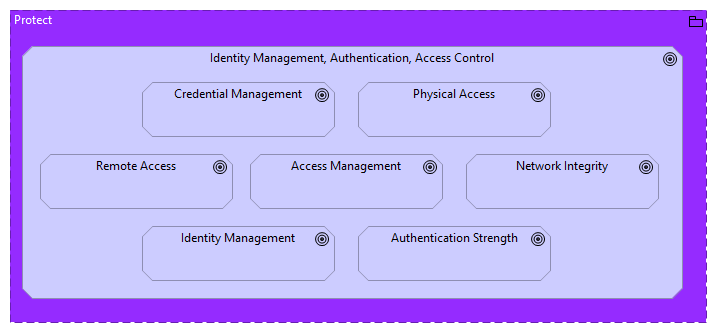
Protect |
Identity Management, Authentication, Access Control |
| |
|
Identity Management, Authentication, Access Control |
Credential Management |
| |
|
Identity Management, Authentication, Access Control |
Physical Access |
| |
|
Identity Management, Authentication, Access Control |
Access Management |
| |
|
Identity Management, Authentication, Access Control |
Remote Access |
| |
|
Identity Management, Authentication, Access Control |
Network Integrity |
| |
|
Identity Management, Authentication, Access Control |
Authentication Strength |
| |
|
Identity Management, Authentication, Access Control |
Identity Management |